
Write something
Pinned
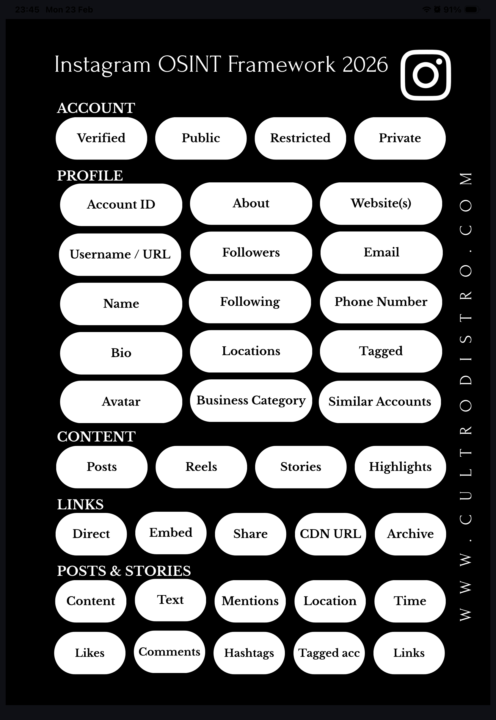
The Instagram OSINT Framework 2026 - An Exclusive Comprehensive Cheat Sheet
📌 INSTAGRAM OSINT FRAMEWORK 2026 In due diligence and compliance investigations, social media is often overlooked as an intelligence source. Instagram alone can reveal significant information about a subject, if you know where to look. This framework covers every layer. 🔗 All tools & resources referenced in this framework can be found at: • https://www.cultrodistro.com • https://www.cultrodistro.com/tools/socials • https://www.cultrodistro.com/tools/images 🔷 ACCOUNT TYPES • Public – fully accessible, crawlable with online tools • Restricted – public but hidden from some users due to content; still crawlable • Private – only username, bio & profile picture visible • Verified – public + Instagram-confirmed identity, usually business accounts 🔷 PROFILE • Account ID – assigned at creation, never changes, findable via crawlers or F12 > search “account ID” • Bio & name – often contains location hints, hobbies, personal clues • About section – shows account creation date and previous usernames • Avatar – can be enlarged and extracted for analysis • Followers/following – reveals interests and network connections • Location tags – verifiable via reverse image search or geolocation • Business profiles – expose category, website, email, phone number • Tagged posts & suggested accounts – additional context 🔷 CONTENT • Posts & Reels – permanent/semi-permanent visual content • Stories – disappear after 24h unless saved as Highlights • Highlights – thematically organized, often revealing 🔷 LINKS • Direct links – go straight to content • Embedded links – shareable on other platforms • Share links – ⚠️ contain metadata exposing your identity; avoid professionally • CDN URLs – bypass Instagram’s interface, ideal for archiving via archive.org 🔷 POSTS & STORIES • Reverse image search visuals • Analyze text for writing style, cultural clues, education level
Pinned
🧽 Content Removal: How to Remove Unwanted Content from the Web
🥀 Your past doesn’t have to haunt your digital present. Maybe it’s an intimate photo shared without your consent. Perhaps it’s outdated information that no longer represents who you are. Or it could be content that violates your privacy, defames your character, or infringes on your copyright. Whatever the case, unwanted content online can derail job opportunities, damage relationships, and cause immense emotional distress. 🦾 The good news? You’re not powerless. The internet may feel permanent, but there are proven pathways to reclaim your digital narrative. This guide cuts through the confusion and shows you exactly how to remove harmful content from search engines, social media platforms, and websites, step by step. Visit https://www.cultrodistro.com/tools/browsing for the direct links. 👙 Non-Consensual Intimate Content Stop NCII specializes in removing intimate images from partner sites including Pornhub, OnlyFans, and major social media platforms. They create a digital fingerprint of your images without viewing them, then share it with platforms for automatic detection and removal. Google offers several removal pathways: 📩 Personal Information - Remove doxxing content, financial information, contact details, and images containing personal data from search results. 📩 Legal Issues - Submit removal requests for content that violates laws in your jurisdiction, including defamatory or privacy-violating material. 📩Outdated Content - Remove information that’s been updated or deleted from the original source but still appears in Google’s cache or search results. ©️ DMCA Takedown Requests For copyright infringement, file a DMCA takedown notice directly with platforms (free) or through paid services. Include identification of your copyrighted work, location of infringing material, contact information, and a good faith statement. 👨🏻💼 Contact Website Owners Directly Use WHOIS databases to find website owner contact information. A direct removal request is often the fastest solution. For international domains, the IANA Root Zone Database provides information about top-level domain operators.
🔪 EDC Knife or Weapon: The Legal Linguistic Trap
The Dutch police recently announced a “record number” of 2,300 weapon seizures from minors in 2025, claiming a surge from 1,800 in 2022. However, a closer look at their own data and imagery reveals a process of statistical laundering that criminalizes utility tools and targets marginalized youth through demographic profiling. The Example: A Tool Framed as a Threat The police often use professional photography to illustrate these “dangerous weapons”. In one prominent image, an officer holds a black folding knife. An OSINT analysis identifies this object as the Walther Emergency Rescue Knife (ERK). Legal Status: This is a commercially available tool sold legally in stores. Function: It is specifically designed as a life-saving tool, featuring a glass breaker and a belt cutter for emergency situations. Technical Compliance: According to the official Customs (Douane) flowchart, this knife is legally NOT a weapon because it has only one cutting edge and is under 28 cm in length. By using a rescue tool to represent “prohibited weapons,” the police perform “Linguistic Capture”—redefining a neutral utility object as a criminal instrument before any legal investigation into its use has occurred. Statistical Laundering and Enforcement Intensity The police admit they do not know the “true scope” of weapon possession among youth; their numbers only reflect how often they choose to seize items. Furthermore, they acknowledge that the “increase” is partly due to changes in counting methods and “increased attention” from officers. The Trap: This creates an unfalsifiable loop. Any seizure—even of a legal rescue tool—is used as evidence that a “weapon problem” exists, which in turn justifies more seizures. This isn’t a measure of crime; it is a measure of enforcement intensity. Legal Discrimination: The Double Standard The sources highlight a deep systemic bias in how the law is applied. Under Category IV sub 7 of the Weapons Act, a legal tool only becomes a “weapon” based on the “nature and circumstances” of its discovery. This grants police total discretion to decide who is a criminal:
0
0

Welcome! Ask me anything
👋 A huge welcome to all the new members! I’m so glad you’re here! I built this space to share what I’m learning, what I’m working on, and the OSINT rabbit holes and questions I’m chewing on. The more I hear from you, the better it gets. To kick things off: what’s one thing you’d love to see more of here? Could be a topic, a type of OSINT deep-dive, a resource, a specific question, anything goes. Drop your thoughts below 👇 or send me a message!
📈 OSINT everything?
Shiny Hunters breached Dutch universities. Real names, social security numbers, dates of birth.all sitting in leaked databases now. This adds to a growing pool of stolen data accessible to OSINT professionals and hackers alike. Earlier this year, Odido got hit. KPN got hit in December. Prior other universities got hit. So where’s the line between legitimate open source intelligence and accessing stolen data? Traditionally OSINT meant publicly available information: Google searches, government registers, the Wayback Machine. But now leaked databases from telecom breaches, university data dumps, they’re becoming part of the landscape. If you’re doing OSINT research or investigations, how do you even know if your sources are legitimately public or stolen? The answer matters, because this trend isn’t slowing down.
1-30 of 49
powered by

skool.com/huisvestnl-3698
Get started in OSINT and learn how to find out about anything and anyone online, professionally.
Suggested communities
Powered by
