Activity
Mon
Wed
Fri
Sun
May
Jun
Jul
Aug
Sep
Oct
Nov
Dec
Jan
Feb
Mar
Apr
What is this?
Less
More
Owned by Cultro
Get started in OSINT and learn how to find out about anything and anyone online, professionally.
Memberships
Fraser AI
293 members • Free
CC Strategic AI
3.3k members • $47/month
Vibe Labs
1.1k members • Free
Cyber RedFlag
3 members • Free
The AI Advantage
115.2k members • Free
Heroic Intelligence Map Guild
5 members • Free
44 contributions to OSINT Detective Skool
⚓️ €5 tracker, €500M warship, zero surprises for anyone doing OSINT.
Last week, Dutch broadcaster Omroep Gelderland tracked the location of Zr. Ms. Evertsen, a Dutch air-defense frigate escorting France’s Charles de Gaulle carrier in the eastern Mediterranean, by mailing a generic Bluetooth tracker (basically a cheap AirTag clone, the kind you buy on AliExpress for five euros) inside a greeting card via military postal service. The tracker piggybacked on Apple’s Find My network, relaying its position through any nearby iPhone. From the sorting center in the Netherlands to Crete to 24 hours at sea, the frigate’s route was mapped in real time. The security establishment panicked. Defensie banned greeting cards containing batteries from being sent to the ship. The minister briefed parliament. But this isn’t news. It’s confirmation.The Evertsen was trackable from the moment it left Den Helder. You could find that ship without the tracker. Most military vessels operating outside active conflict zones are already fully exposed through public infrastructure: AIS broadcasts (MarineTraffic, VesselFinder), crew social media leakage (Strava, LinkedIn), port webcams, satellite imagery, and vessel registries. The Bluetooth story got traction because it’s visceral. A postcard, five euros, a journalist. It feels like a breach because it is one. But it’s a symptom. The disease is operational security built on the assumption that a modern warship can hide in the most observed maritime zone on the planet. It can’t. For compliance and intel professionals: this is a live case study in exposure collapse. The infrastructure
2026 is a bad year to have a weak password: Data breaches on the rise
Phishing still works. And automation and AI are making it easier and more scalable for hackers to use stolen data for fraud. The real risk after a breach? Credential stuffing. Attackers take your leaked password and automatically try it on your bank, your email, your Amazon, your Apple ID. Automated, at scale, within hours. I built a free toolkit with a step-by-step approach to make this nearly impossible: → Check if your data was leaked (via HaveIBeenPwned, IntelX and IntelBase) → Fix your password management — the 4 pillars → Secure your accounts in the right order (banking first) → Set up alerts and plus-addressing to trace future leaks instantly This toolkit was written for the Odido / T-Mobile NL breach, but the steps apply to any data breach. This is exactly what OPSEC is about — and why we have a full free course on it in this community. If you haven't started OPSEC 101 yet, this is your wake-up call. One reused password can be all it takes. Start today. 🔗 https://www.cultrodistro.com/blog/odido-data-breach-toolkit
0
0
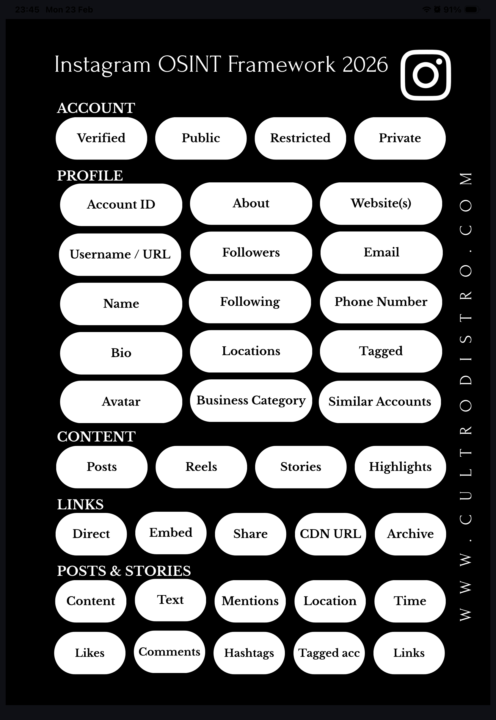
The Instagram OSINT Framework 2026 - An Exclusive Comprehensive Cheat Sheet
📌 INSTAGRAM OSINT FRAMEWORK 2026 In due diligence and compliance investigations, social media is often overlooked as an intelligence source. Instagram alone can reveal significant information about a subject, if you know where to look. This framework covers every layer. 🔗 All tools & resources referenced in this framework can be found at: • https://www.cultrodistro.com • https://www.cultrodistro.com/tools/socials • https://www.cultrodistro.com/tools/images 🔷 ACCOUNT TYPES • Public – fully accessible, crawlable with online tools • Restricted – public but hidden from some users due to content; still crawlable • Private – only username, bio & profile picture visible • Verified – public + Instagram-confirmed identity, usually business accounts 🔷 PROFILE • Account ID – assigned at creation, never changes, findable via crawlers or F12 > search “account ID” • Bio & name – often contains location hints, hobbies, personal clues • About section – shows account creation date and previous usernames • Avatar – can be enlarged and extracted for analysis • Followers/following – reveals interests and network connections • Location tags – verifiable via reverse image search or geolocation • Business profiles – expose category, website, email, phone number • Tagged posts & suggested accounts – additional context 🔷 CONTENT • Posts & Reels – permanent/semi-permanent visual content • Stories – disappear after 24h unless saved as Highlights • Highlights – thematically organized, often revealing 🔷 LINKS • Direct links – go straight to content • Embedded links – shareable on other platforms • Share links – ⚠️ contain metadata exposing your identity; avoid professionally • CDN URLs – bypass Instagram’s interface, ideal for archiving via archive.org 🔷 POSTS & STORIES • Reverse image search visuals • Analyze text for writing style, cultural clues, education level
1 like • Feb 25
@Samee Ul Bari Thanks for asking. OSINT = finding info on someone using stuff that's already publicly available (no hacking needed). This framework is basically a checklist for Instagram. It tells you everything you can dig up from a profile, Like for example: their real name, email, phone number, locations they've visited, who they hang out with, and even deleted posts. All from just an Instagram account. Use this professionally (investigations, due diligence, compliance, etc.), not to stalk on people personally. Make sure it aligns with the rules of this Skool and the laws in your country.
Epstein Scoop: Don’t Move the Body
📚 The Epstein Library Search That Started With a Broken Link Alert Working in Anti Money Laundering, I run continuous screening on Politically Exposed Persons (PEPs) under EU Anti-Money Laundering rules. My system monitors links automatically. 📩 How It Actually Started I got an alert by email: “Link broken - UN OCHA leadership page.” Not unusual. Websites change. But when I clicked through… “Access denied.” Wait. Not a 404. Not “page moved.” Access denied on what used to be a public UN leadership page? That’s the kind of thing that makes an OSINT Detective curious. 😣 It’s also decidedly inconvenient because AML analysts have to check whether the UBO or client is a PEP, and now access is denied on the leadership page, analysts can’t do their job without using extra OSINT tools. Which is weird, since it’s a publicly exposed person holding a position at the UN. 🐇 Down The Rabbit Hole: Pulled up the Wayback Machine. Sure enough - the page was public for years. Leadership bios, photos, organizational charts. Then suddenly - locked. So I did what you do when something feels off: searched the DOJ’s Epstein Library. “OCHA” - multiple hits. “Martin Griffiths” (former Under-Secretary-General) - hits there too. ✅ Reality Check: The mentions are completely routine. Humanitarian coordination documents. Normal UN references. Nothing illegal. Nothing even interesting, honestly. 🎭 But Here’s The Irony: Without that broken link alert? I never would have looked. The OCHA page would’ve been just another line item in continuous monitoring. Green checkmark. Move on. The restriction itself triggered the investigation. 🔨What My Tools Found: ✓ Automated link checker - flagged the broken/restricted URL ✓ Continuous screening alerts - notified me of the change✓ Wayback Machine - showed the history ✓ Curiosity - led me to the Epstein Library 🧠 The Lesson: When you restrict previously public information in 2026, you’re not hiding it. You’re highlighting it. Automated compliance systems notice when things change. They send alerts. Those alerts make people investigate.
🧽 Content Removal: How to Remove Unwanted Content from the Web
🥀 Your past doesn’t have to haunt your digital present. Maybe it’s an intimate photo shared without your consent. Perhaps it’s outdated information that no longer represents who you are. Or it could be content that violates your privacy, defames your character, or infringes on your copyright. Whatever the case, unwanted content online can derail job opportunities, damage relationships, and cause immense emotional distress. 🦾 The good news? You’re not powerless. The internet may feel permanent, but there are proven pathways to reclaim your digital narrative. This guide cuts through the confusion and shows you exactly how to remove harmful content from search engines, social media platforms, and websites, step by step. Visit https://www.cultrodistro.com/tools/browsing for the direct links. 👙 Non-Consensual Intimate Content Stop NCII specializes in removing intimate images from partner sites including Pornhub, OnlyFans, and major social media platforms. They create a digital fingerprint of your images without viewing them, then share it with platforms for automatic detection and removal. Google offers several removal pathways: 📩 Personal Information - Remove doxxing content, financial information, contact details, and images containing personal data from search results. 📩 Legal Issues - Submit removal requests for content that violates laws in your jurisdiction, including defamatory or privacy-violating material. 📩Outdated Content - Remove information that’s been updated or deleted from the original source but still appears in Google’s cache or search results. ©️ DMCA Takedown Requests For copyright infringement, file a DMCA takedown notice directly with platforms (free) or through paid services. Include identification of your copyrighted work, location of infringing material, contact information, and a good faith statement. 👨🏻💼 Contact Website Owners Directly Use WHOIS databases to find website owner contact information. A direct removal request is often the fastest solution. For international domains, the IANA Root Zone Database provides information about top-level domain operators.
1-10 of 44
Active 20h ago
Joined Aug 19, 2025

