
Write something
Open Claw Try it!
Know when your parents told you not to do something and you did it anyways? That's how I feel about people who aren't security experts that play with open claw. @Diane McCracken and I were having fun with this discussion so I thought I would share my artistic interpretation of what will most likely happen to the casual user. 😆

[SAVE] Claude Code Commands Reference ✅
Here's the current up-to-date list. Markdown file included. You can keep yourself updated at the Claude official site. Claude Code Commands Reference Source: https://code.claude.com/docs/en/commands Fetched: 2026-05-13 Commands control Claude Code from inside a session. They provide a quick way to switch models, manage permissions, clear context, run a workflow, and more. Type / to see every command available to you, or type / followed by letters to filter. A command is only recognized at the start of your message. Text that follows the command name is passed to it as arguments.
![[SAVE] Claude Code Commands Reference ✅](https://assets.skool.com/f/f1f8713c199d4c3b994a02e649d607de/fc4514ee45a244649805c1d4f8c37e084790fb2845ec499ab91d4988ac234465-md.png)
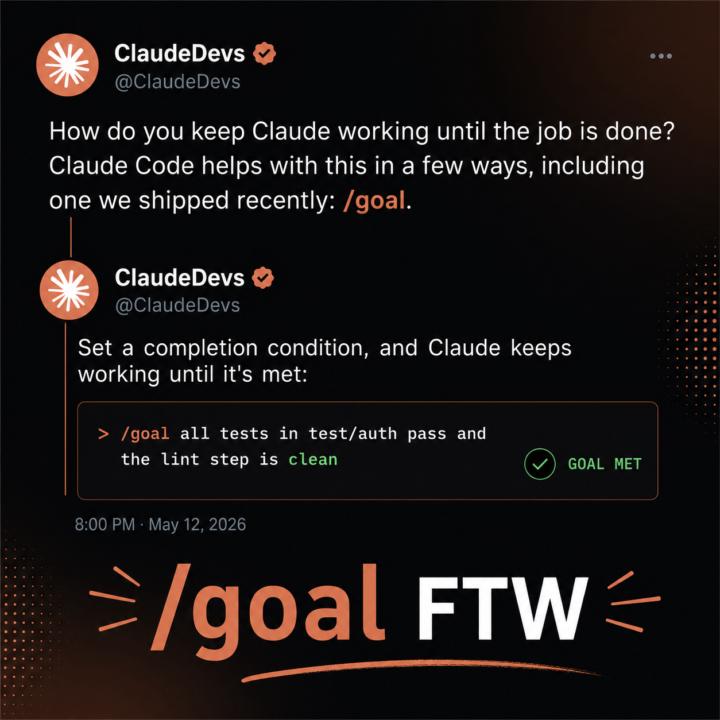
Claude Code /goal
The /goal command in Claude Code sets a completion condition that keeps Claude working autonomously across multiple turns until that condition is met. After you type /goal followed by your desired end state (like "all tests pass" or "build exits 0"), a small fast model checks after each turn whether the condition holds. If not, Claude automatically starts another turn without waiting for you to prompt it, effectively creating a persistent loop—plan, act, test, review—until your goal is verifiably complete. This transforms Claude from responding to individual prompts into an autonomous agent that can work on substantial tasks with measurable outcomes, like migrating code until tests pass or refactoring until the build succeeds. @Diane McCracken @Michael Wacht @Mike Thomson @Mike AI Consultant @Nick Mohler @Antonio Capunzo @Pacita Florida @Dimi Tse @R S @John Romano @Kesnel Chery @Matt Kaplan
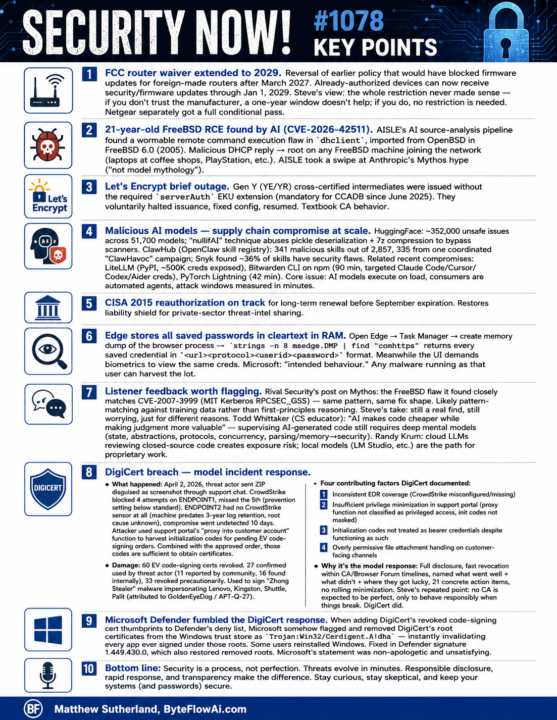
Security Now episode #1078 Key Points
Security Now! #1078 — Key Points ================================= FCC ROUTER WAIVER EXTENDED TO 2029 Reversal of earlier policy that would have blocked firmware updates for foreign-made routers after March 2027. Already-authorized devices can now receive security/firmware updates through Jan 1, 2029. Steve's view: the restriction never made sense — if you don't trust the manufacturer, a one-year window doesn't help; if you do, no restriction is needed. Netgear separately got a full conditional pass. 21-YEAR-OLD FREEBSD RCE FOUND BY AI (CVE-2026-42511) AISLE's AI source-analysis pipeline found a wormable remote command execution flaw in dhclient, imported from OpenBSD in FreeBSD 6.0 (2005). Malicious DHCP reply -> root on any FreeBSD machine joining the network (laptops at coffee shops, PlayStation, etc.). AISLE took a swipe at Anthropic's Mythos hype ("not model mythology"). LET'S ENCRYPT BRIEF OUTAGE Gen Y (YE/YR) cross-certified intermediates were issued without the required serverAuth EKU extension (mandatory for CCADB since June 2025). They voluntarily halted issuance, fixed config, resumed. Textbook CA behavior. MALICIOUS AI MODELS — SUPPLY CHAIN COMPROMISE AT SCALE HuggingFace: ~352,000 unsafe issues across 51,700 models. "nullifAI" technique abuses pickle deserialization + 7z compression to bypass scanners. ClawHub (OpenClaw skill registry): 341 malicious skills out of 2,857, 335 from one coordinated "ClawHavoc" campaign. Snyk found ~36% of skills have security flaws. Related recent compromises: - LiteLLM (PyPI, ~500K creds exposed) - Bitwarden CLI on npm (90 min, targeted Claude Code/Cursor/Codex/Aider) - PyTorch Lightning (42 min) Core issue: AI models execute on load, consumers are automated agents, attack windows measured in minutes. CISA 2015 REAUTHORIZATION ON TRACK Long-term renewal expected before September expiration. Restores liability shield for private-sector threat-intel sharing. EDGE STORES ALL SAVED PASSWORDS IN CLEARTEXT IN RAM
Passkeys vs passwords
• A password is like a secret word you type that a website remembers; if someone tricks you into telling it to them, they can pretend to be you. • A passkey is more like a special key stored on your phone or computer that never leaves your device; the website only sees proof that your real key unlocked the door. • Bad guys can steal or guess passwords using fake emails, keyloggers, or leaked databases, but they cannot copy your passkey because it stays locked inside your device. • With passkeys, you usually just tap your fingerprint, look at your camera, or enter a short PIN, so it’s both easier and safer than remembering long, messy passwords. • Until every site uses passkeys, you still need strong, unique passwords in a manager plus MFA, but the goal is to move toward passkeys and stop using passwords over time.

1-30 of 131
powered by

skool.com/ai-for-life-3967
Practical AI training for work and life. Hands-on lessons with Claude,
ChatGPT, and automation tools. Built for people ready to use AI.
Suggested communities
Powered by
