Activity
Mon
Wed
Fri
Sun
Jun
Jul
Aug
Sep
Oct
Nov
Dec
Jan
Feb
Mar
Apr
What is this?
Less
More
Owned by Pavel
Learn AI, automation and security tools reshaping modern SOC and cyber careers.
Memberships
Skoolers
193.1k members • Free
26 contributions to AI Security & Automation
Real Mythos Data
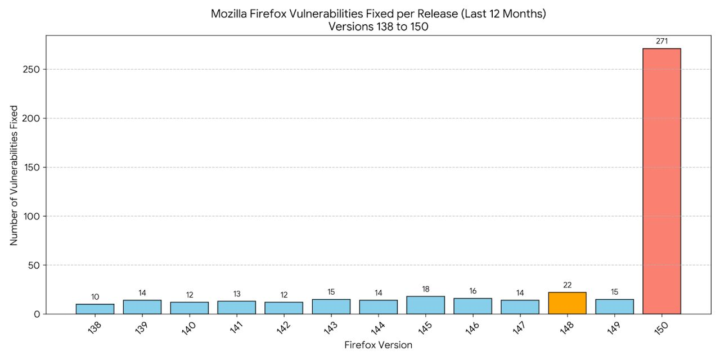
Mozilla released Firefox 150 yesterday, fixing 271 vulnerabilities found with the help of Mythos. Here is a chart of the amount of vulnerabilities they fixed in the previous 12 months of releases. Source: https://lnkd.in/ecwWPden
0
0
📅 Weekly Security Briefing — Apr 13–19, 2026
🚨 Microsoft Patch Tuesday Fixes 167 Flaws & 2 Zero-Days What happened: Microsoft released one of its largest updates ever, fixing 167 vulnerabilities, including two zero-days — one actively exploited in the wild. The most critical is CVE-2026-32201, a SharePoint spoofing flaw that allows attackers to manipulate data and access sensitive information. 🔗 https://www.bleepingcomputer.com/news/microsoft/microsoft-april-2026-patch-tuesday-fixes-167-flaws-2-zero-days/ 📂 13.5 Million McGraw Hill Accounts Leaked in Data Breach What happened: The ShinyHunters group leaked data from 13.5 million McGraw Hill users, reportedly due to a Salesforce misconfiguration. The breach exposed personal data and highlights ongoing risks tied to SaaS misconfigurations and weak cloud access controls. 🔗 https://www.bleepingcomputer.com/news/security/data-breach-at-edtech-giant-mcgraw-hill-affects-135-million-accounts/ 🤖 Frontier AI Models Raise Concerns Over Offensive Capabilities What happened: Policymakers and researchers are raising concerns over increasingly powerful AI systems capable of autonomous vulnerability discovery and exploit chaining. Discussions are underway around leveraging these capabilities defensively, while limiting misuse as models become more capable. 🔗 https://datainnovation.org/2026/04/federal-government-should-partner-with-frontier-ai-labs-on-cybersecurity-defense/ 🕵️♂️ Operation PowerOFF Disrupts Global DDoS-for-Hire Networks What happened: Law enforcement agencies identified 75,000 users of DDoS-for-hire services and seized 53 domains as part of Operation PowerOFF. The coordinated action significantly disrupts access to low-cost attack infrastructure used worldwide.
1
0
📅 Weekly Security Briefing — Mar 30 – Apr 5, 2026
Honestly the last week was insane, so many interesting and scary staff. If you don't read this usually, I would highly recommend reading this week summary. 🛡️ Axios npm Supply Chain Attack Impacts Millions of Developers What happened: A major supply chain attack compromised the widely used Axios npm package, impacting a library with ~100 million weekly downloads. Attackers hijacked a maintainer account and published malicious versions that injected a hidden dependency executing a cross-platform remote access trojan (RAT) during installation. The campaign has been attributed to a North Korean-linked actor, with payloads targeting Windows, macOS, and Linux systems. 🔗 https://www.microsoft.com/en-us/security/blog/2026/04/01/mitigating-the-axios-npm-supply-chain-compromise/ 🤖 DeepLoad Malware Uses AI to Evade Detection What happened: Researchers identified a new malware strain dubbed DeepLoad, which leverages AI model APIs to dynamically generate polymorphic malicious code during execution. By continuously changing its structure and behavior at runtime, the malware can bypass traditional signature-based defenses and adapt in real time to detection mechanisms. 🔗 https://reliaquest.com/blog/threat-spotlight-deepload-malware-pairs-clickfix-delivery-with-ai-generated-evasion/ ☁️ AWS Expands Bedrock Security with Cross-Account Guardrails What happened: AWS announced general availability of cross-account guardrails for Amazon Bedrock, enabling organizations to enforce consistent AI security and governance policies across multiple accounts. This allows centralized control over model behavior, compliance rules, and safety constraints across enterprise-scale AI deployments. 🔗 https://aws.amazon.com/blogs/aws/amazon-bedrock-guardrails-supports-cross-account-safeguards-with-centralized-control-and-management/
AI Supply Chain Attack
If you are using Claude Code, Codex, Gemini or any other tool for coding on your desktop, you might want to pay attention to this. https://www.trendmicro.com/zh_hk/research/26/c/axios-npm-package-compromised.html https://www.huntress.com/blog/supply-chain-compromise-axios-npm-package https://www.sophos.com/en-us/blog/axios-npm-package-compromised-to-deploy-malware I have just woke up, but apparently there has been huge supply chain attack. At the moment I'm working on threat hunting. Here is the KQL hunt query. Might be useful to someone. let TimePeriod = 3d; // Hash IOCs let AxiosIOCMD5 = dynamic([ "21d2470cae072cf2d027d473d168158c", "db7f4c82c732e8b107492cae419740ab", "7658962ae060a222c0058cd4e979bfa1", "089e2872016f75a5223b5e02c184dfec", "04e3073b3cd5c5bfcde6f575ecf6e8c1", "7a9ddef00f69477b96252ca234fcbeeb", "9663665850cdd8fe12e30a671e5c4e6f", "8c782b59a786f18520673e8d669e3b0a" ]); let AxiosIOCSHA1 = dynamic([ "2553649f2322049666871cea80a5d0d6adc700ca", "d6f3f62fd3b9f5432f5782b62d8cfd5247d5ee71", "07d889e2dadce6f3910dcbc253317d28ca61c766", "b0e0f12f1be57dc67fa375e860cedd19553c464d", "978407431d75885228e0776913543992a9eb7cc4", "a90c26e7cbb3440ac1cad75cf351cbedef7744a8", "13ab317c5dcab9af2d1bdb22118b9f09f8a4038e", "59faac136680104948e083b3b67a70af9bfa5d5e", "ae39c4c550ad656622736134035f17ca7a66a742" ]); let AxiosIOCSHA256 = dynamic([ "5bb67e88846096f1f8d42a0f0350c9c46260591567612ff9af46f98d1b7571cd", "59336a964f110c25c112bcc5adca7090296b54ab33fa95c0744b94f8a0d80c0f", "58401c195fe0a6204b42f5f90995ece5fab74ce7c69c67a24c61a057325af668", "e10b1fa84f1d6481625f741b69892780140d4e0e7769e7491e5f4d894c2e0e09", "f7d335205b8d7b20208fb3ef93ee6dc817905dc3ae0c10a0b164f4e7d07121cd", "617b67a8e1210e4fc87c92d1d1da45a2f311c08d26e89b12307cf583c900d101",
0
0
1-10 of 26
@pavel-hrabec-4806
SOC Architect and team leader using custom security AI agents to protect sectors such as government, banking, production and more.
Active 1h ago
Joined Oct 21, 2025
INTJ

