Activity
Mon
Wed
Fri
Sun
May
Jun
Jul
Aug
Sep
Oct
Nov
Dec
Jan
Feb
Mar
Apr
What is this?
Less
More
Memberships
CISSP Study Group
2.1k members • Free
22 contributions to CISSP Study Group
Chat with Claude about YOUR cissp.app stats and exam readiness
You can now access our 3,600+ CISSP practice questions, as well as YOUR personal data from cissp.app directly inside Claude. Correct / incorrect answers, mock exams taken, even the amount of time spent per question, you can get all that fed to Claude for better analysis on your data. Ask it to quiz you, check your answers, and get the same Manager Logic explanations you're used to from cissp.app without leaving your AI chat. cissp.app subscribers get unlimited questions plus your personal study stats, weak area analysis, and exam readiness scoring right inside Claude. We're the first and only CISSP prep tool that has this. How to set it up (30 seconds): 1. Open Claude at claude.ai (free account works) 2. Click the hamburger menu → Settings → Connectors 3. Click "Add" and paste this URL: https://cissp-mcp-server.cissp.workers.dev/mcp 4. Done. Start chatting. Examples of what you can ask: - "Give me a hard CISSP question about access control" - "Quiz me on Domain 4 — Network Security" - "I think the answer is B" (it checks and explains why) - "What are my weakest CISSP domains?" (subscribers) - "Am I ready for the exam?" (subscribers) Try it and let me know what you think in the comments.
CISSP Practice Question (Domain 8: Software Development Security)
Your development team is using an AI coding assistant that auto-suggests code snippets sourced from public repositories. A senior engineer discovers some suggestions closely mirror a competitor's proprietary library. What should you do FIRST? A. Engage legal counsel to evaluate intellectual property exposure B. Ban all AI coding assistants until a formal usage policy is approved C. Restrict the tool's access to internal repositories and require peer code review D. Implement software composition analysis to flag externally sourced code Come back for the answer tomorrow, or study more now!
CISSP Practice Question!
During a penetration test, the red team discovers a critical vulnerability in a production system that could allow full privilege escalation. From a CISSP perspective, what’s the right next step, should they exploit it fully to prove impact, or stop short and document the finding? How do you balance business risk, liability, and the test’s objectives?
Practice Question!
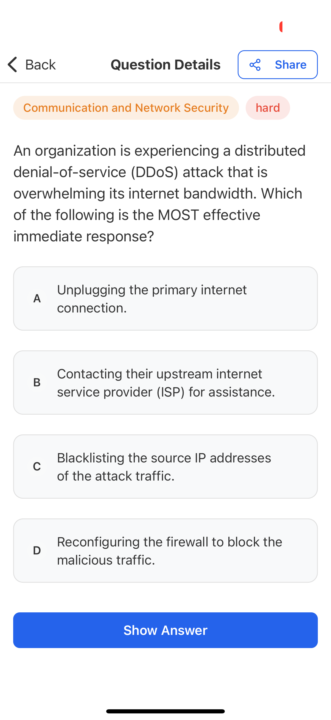
An organization is experiencing a distributed denial-of-service (DDoS) attack that is overwhelming its internet bandwidth. Which of the following is the MOST effective immediate response? A Unplugging the primary internet connection. B Contacting their upstream internet service provider (ISP) for assistance. C Blacklisting the source IP addresses of the attack traffic. D Reconfiguring the firewall to block the malicious traffic.
Practice Questions
What is the MOST important element when considering the effectiveness of a training program for Business Continuity (BC) and Disaster Recovery (DR)? A. Management support B. Consideration of organizational need C. Technology used for delivery D. Target audience
1-10 of 22
Active 2d ago
Joined Mar 10, 2025
United Arab Emirates
Powered by


