X Space has a new home.
Spaces is moving. New time: Thursdays at 6pm ET starting this week. Same format, same conversations. Just a better slot. See you there. 👽
0
0
Just dropped the first free course in the Classroom.
Creator GTM Breakdowns - 4 clips breaking down go-to-market strategy for creators. Real tactics, no fluff. First lesson is live. Check the Classroom tab.
0
0
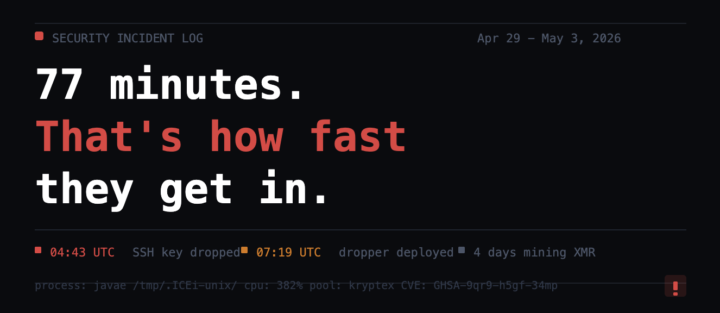
77 minutes. That's how fast an attacker gets in through an unpatched Next.js container.
77 minutes. That's how fast an attacker got inside our server. A crypto miner ran silently for 4 days before I caught it. Mining Monero. CPU pegged at 382%. Hiding as a Java process in /tmp/.ICEi-unix/. Hit a container I was running with an outdated Next.js build. Critical RCE vulnerability, CVE GHSA-9qr9-h5gf-34mp, patched in 15.5.15+. Bots are scanning for it constantly. Did the forensics properly before touching anything. Verified the attacker never escaped the container. ClawMarket was never affected. Users were never at risk. Then I built a heartbeat cron that runs every 10 minutes checking for known miner signatures, sustained CPU spikes, and unapproved containers. Fires an admin alert on detection. Found out via CPU graphs this time. Never again. The lessons that stuck: Docker doesn't mean safe. An outdated package on a public port is an open door. Your git config is not a safe place for credentials. Forensics before cleanup, always. Building in public means sharing the ugly parts too. This is one of them.
0
0
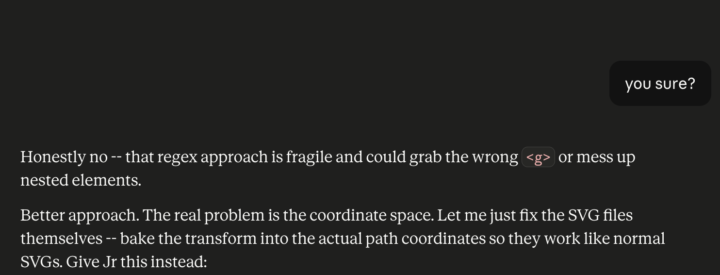
"You sure?" is now part of my workflow
Asked Claude if it was sure about its own approach. It said no. Then gave me a completely different and better solution. Most people just take the first answer and run with it. "You sure?" is now part of my workflow. Two words that have saved me hours of debugging broken code. Always pressure test the first answer.
Claude told me: "Real Talk"
I've never used that line in my life. Claude says "Real Talk" I respond because i'm laughing "Real Talk" Now Claude is throwing "Real Talk" at me about once a day.
0
0

1-16 of 16
powered by
skool.com/neon-aliens-ai-1514
We help founders build AI content systems so they stop being the bottleneck in their own marketing. No hype. Just what works. 👽
Suggested communities
Powered by

