Activity
Mon
Wed
Fri
Sun
Jul
Aug
Sep
Oct
Nov
Dec
Jan
Feb
Mar
Apr
May
What is this?
Less
More
Memberships
BowTiedCyber Hoodies
3.9k members • Free
1083 contributions to BowTiedCyber Hoodies
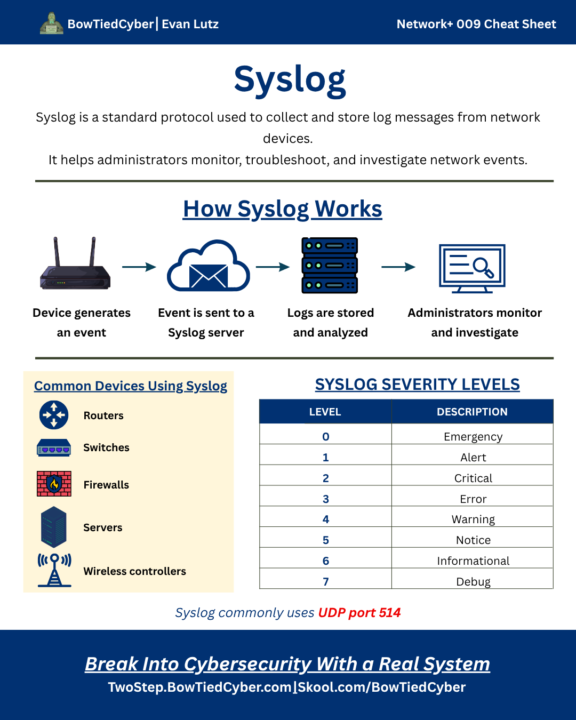
Network+ Cheatsheet - Syslog
Most network issues leave clues. Syslog helps teams collect, centralize, and analyze those clues before they become bigger problems. It tell stories. Learn how to read them.
0
0
Network+ Daily 🧠
A network administrator is designing a network closet and wants a location where backbone cabling from multiple IDFs terminates and connects to core network equipment. Which of the following locations should be used?
Poll
Cast your vote
0 likes • 5h
Answer: B. Main Distribution Frame (MDF) Explanation: The Main Distribution Frame (MDF) serves as the central connection point for a building or campus network. It typically houses core switches, routers, and backbone cabling connections from multiple IDFs. An IDF connects end-user devices and local switches, the demarcation point is where the provider's network connects to the customer's network, and a screened subnet (DMZ) is a security zone for public-facing systems.
Skills opened the door. Certifications added credibility.
Big congrats to our bootcamp student for passing CSAP 🔥 Now he's heading into an interview for an entry-level cybersecurity role with city government. Skills. Certifications. Momentum. One step at a time. 👏
(Remote) Technical Support Specialist | pay: $47k/yr.
Location: Troy, MI This position is located within the Support Department of 365 Retail Markets, and reports to the Support Supervisor. You will play a key role in ensuring that our clients receive a consistent and exceptionally positive experience at all times. Your primary role will focus on maintaining uninterrupted, optimal performance of the 365 product suite at all times across a diverse installation base. You should enjoy tackling unobvious problems, working with time-sensitive clients of varying technical expertise, and in implementing systemic solutions that ensure localized issues are not repeated. Responsibilities - Provide technical system and user support by responding to calls and email requests for technical support in a timely manner - Diligently manage client cases within Zendesk, and communicate any perceived delays to management immediately upon identification - Document, track, and monitor problems to ensure a timely resolution and appropriate follow-up with clients - Assess issues and escalate, if needed, to higher levels of client support - Resolve technical problems, detect patterns of issues, and communicate via the defined escalation path (including services leadership) regarding persistent issues - Assist other department employees in troubleshooting difficult or time-sensitive problems - Configure client equipment both locally and remotely - Maintain your knowledge and expertise by learning new and evolving technologies and by achieving appropriate industry and professional certifications - Contribute to continuous improvement of the client experience by providing suggestions for the betterment of technical practices - Workweek includes Saturday & Sunday shift in schedule, with 2 days off during the weekdays - Other duties as assigned by Supervisor Requirements - 1-2 years experience handling high-end clients with the ability to demonstrate proper service recovery steps or a commensurate combination of education, certifications, and experience - Proficient with Ubuntu or other Linux distribution highly desired - Solid understanding of mobile environments including Android and iOS, including development and logging tools - Solid understanding of Windows 10 environment including device drivers, event viewer, and error reporting - Experience working with advanced software issues that require root cause analysis - Experience maintaining small networks. Network+ a bonus, but not necessary - Exposure to SQL commands a bonus - Able to work independently and efficiently to meet deadlines - Able to promptly answer support related email, phone calls and other electronic communications - Self-motivated, detail-oriented and organized - Ability to learn new technologies quickly and deal with ambiguity - Proficient in Internet related applications such as email clients, FTP clients and web browsers - Proficient in the entire Microsoft Office suite (Word, Excel, Outlook, PowerPoint) - Excellent communication (oral and written), interpersonal, organizational, and presentation skills using appropriate vocabulary and grammar to obtain and convey information
(Remote) Cyber Security Analyst
Location: United States THE ROLE You'll be responsible for monitoring, detecting, and responding to security threats across the environment — working across SIEM, EDR, and vulnerability management tooling to keep the organisation secure. RESPONSIBILITIES Monitor SIEM platforms and security dashboards for threats and anomalous activity Triage and analyse alerts, separating genuine incidents from false positives Lead and support incident response — containment, eradication, recovery, and post-incident review Conduct vulnerability scans, prioritise findings by risk, and track remediation Threat hunt across the enterprise environment and operationalise threat intelligence Produce clear reporting for both technical and non-technical stakeholders Support compliance activities across frameworks such as NIST CSF, SOC 2, or HIPAA REQUIRED SKILLS & EXPERIENCE 2–4+ years in a cyber security analyst or SOC analyst role Hands-on experience with SIEM platforms (Splunk, Microsoft Sentinel, QRadar) Strong understanding of network protocols, TCP/IP, firewalls, and IDS/IPS Experience with EDR tooling (CrowdStrike, SentinelOne, Microsoft Defender) Familiarity with cloud security across AWS, Azure, or GCP Strong analytical skills and ability to communicate findings clearly Full right to to work in the US without sponsorship NICE TO HAVE Certifications: Security+, CySA+, CEH, GCIA, GCIH or equivalent Scripting ability in Python, PowerShell, or Bash Exposure to SOAR platforms and threat intelligence tooling Knowledge of MITRE ATT&CK and the Cyber Kill Chain Experience in a regulated sector (financial services, healthcare, government/DoD) Apply today to make it count! Comment “JOB” and I’ll send you the link to apply!
0
0
1-10 of 1,083

